MySQL Database Repair 1
How to Resolve Log Sequence Number (LSN) Mismatch Issue in MySQL
The LSN (Log Sequence Number) is a unique incremental value which is… Continue reading How to Resolve Log Sequence Number (LSN) Mismatch Issue in MySQL
How to Fix Corrupted Foreign Keys in MariaDB?
Foreign key is one of the components of the MariaDB database. Also… Continue reading How to Fix Corrupted Foreign Keys in MariaDB?
How to Repair Corrupt MySQL Database and Restore Data after MYD File Loss?
MYD (stands for MySQL Data) files are used by MySQL for storing… Continue reading How to Repair Corrupt MySQL Database and Restore Data after MYD File Loss?
How to Restore Old MySQL Databases to New XAMPP Installation?
You usually need to install a new server when you’re facing issues… Continue reading How to Restore Old MySQL Databases to New XAMPP Installation?
How to Troubleshoot MySQL Docker Errors and Ensure Data Integrity?
Docker is a platform used to share and install applications quickly. It… Continue reading How to Troubleshoot MySQL Docker Errors and Ensure Data Integrity?
Fix “Missing FILE_CREATE, FILE_DELETE, or FILE_MODIFY before FILE_CHECKPOINT” Error
The error “Missing FILE_CREATE, FILE_DELETE, or FILE_MODIFY before FILE_CHECKPOINT” occurs when the… Continue reading Fix “Missing FILE_CREATE, FILE_DELETE, or FILE_MODIFY before FILE_CHECKPOINT” Error
Troubleshooting MySQL Error 145 (HY000)
You may encounter the “error 145: Table ‘/dbname/tablename’ is marked as crashed… Continue reading Troubleshooting MySQL Error 145 (HY000)
How to Fix MySQL Error 1030: Got Error 127 from Storage Engine?
The error 1030, also called ER_GET_ERRNO, is an error related to the… Continue reading How to Fix MySQL Error 1030: Got Error 127 from Storage Engine?
How to Fix MySQL Error Code 144?
The MySQL error code 144 indicates that a table is crashed and… Continue reading How to Fix MySQL Error Code 144?
How to Fix MySQL Error 145?
MySQL, developed by Oracle, is nowadays one of most popular database management… Continue reading How to Fix MySQL Error 145?
How to Use MySQL’s Inbuilt Tools to Repair MySQL Database?
How to Use Mysqlcheck Command in MySQL to Repair Databases?Mysqlcheck is a… Continue reading How to Use MySQL’s Inbuilt Tools to Repair MySQL Database?
How to Check Database Corruption in MySQL?
You can use the error log files to check if a MySQL… Continue reading How to Check Database Corruption in MySQL?
Database Page Corruption on Disk or a Failed File Read of a Page in MySQL
One of the important tasks of IT administrators is to constantly verify… Continue reading Database Page Corruption on Disk or a Failed File Read of a Page in MySQL
[Fixed] MySQL innodb_force_recovery is Not Working Properly
Whether you are running MySQL on a Linux or Windows machine, forcing… Continue reading [Fixed] MySQL innodb_force_recovery is Not Working Properly
How to Repair MySQL Database using phpMyAdmin?
When trying to open a corrupt MySQL database, you may receive any… Continue reading How to Repair MySQL Database using phpMyAdmin?
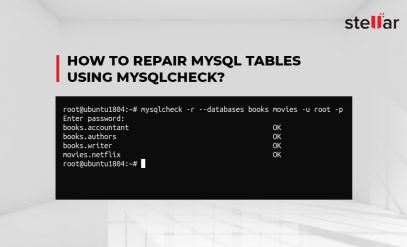
How to Repair MySQL Tables Using Mysqlcheck
Occasionally, you may need to repair corruption in MySQL tables. Corruption in… Continue reading How to Repair MySQL Tables Using Mysqlcheck
How to Recover InnoDB Table Data From Corrupt ibdata1 File in MySQL Server?
In MySQL InnoDB storage engine, ibdata1 is a single system tablespace data… Continue reading How to Recover InnoDB Table Data From Corrupt ibdata1 File in MySQL Server?
How to Fix MySQL Database Error “Incorrect Key File for Table”
You may encounter the MySQL error ‘Incorrect Key File for Table’ when… Continue reading How to Fix MySQL Database Error “Incorrect Key File for Table”